The Trillian Team Talks
 |
On-premise vs cloud use cases for secure instant messaging
When should you opt for cloud-based tools and services, and when is on-prem the right way to go? We run through three use cases to find out.
|
 |
Three disastrous examples of delivering company news (and how to never repeat those mistakes)
From driving forklifts into wet concrete to throwing staplers, here are a few cautionary tales to guide your internal communications processes.
|
 |
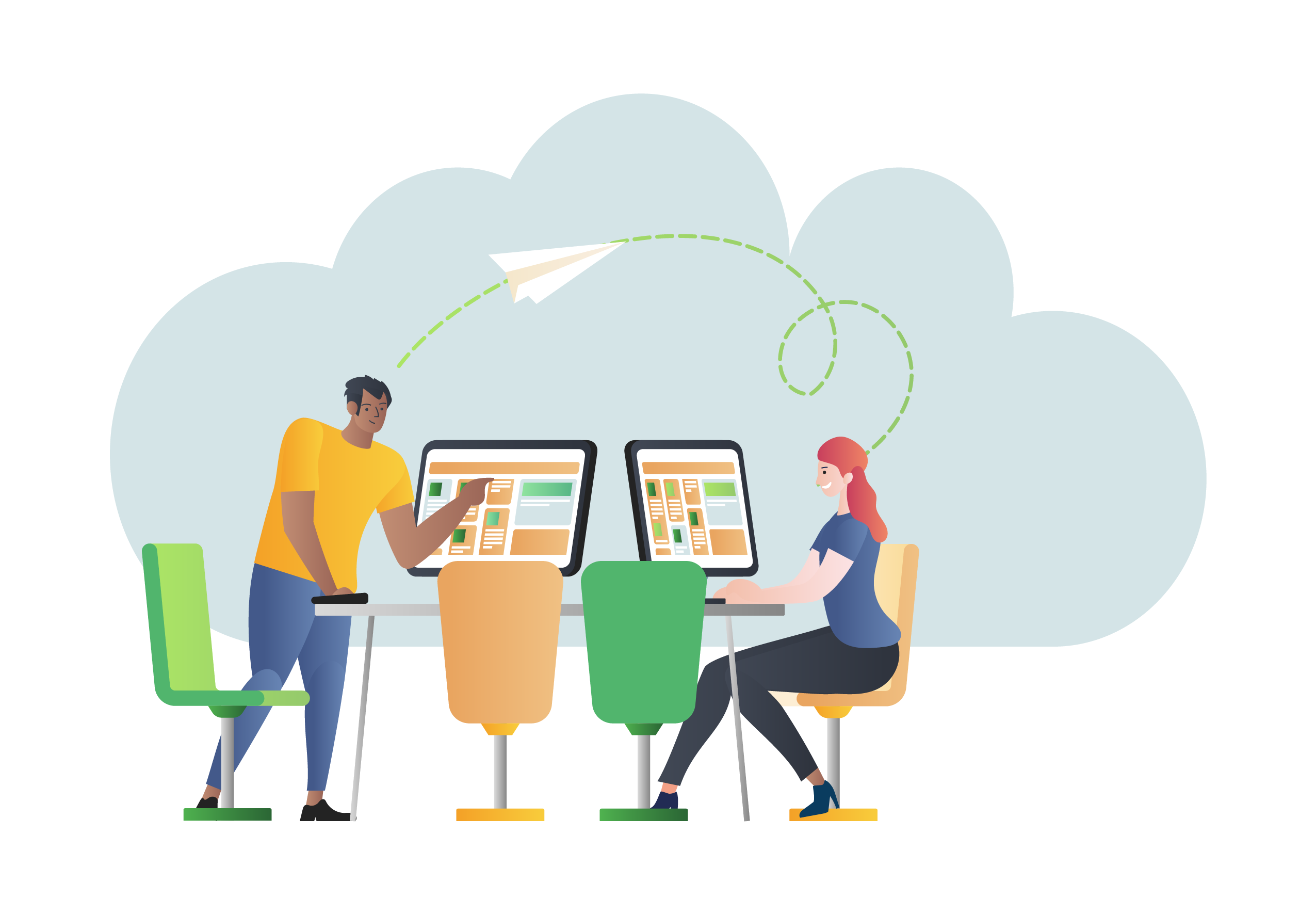
Introducing Trillian Calls: 1:1 video calls and screen sharing
We're pleased to announce Trillian 6.5 for Windows, including the new Trillian Calls feature! Say it face-to-face with simple and secure video calls and screen sharing, now available in Trillian 6.5 for Windows.
|
 |
12 tone of voice tips for different types of business conversations
Different types of business conversations benefit from specific tones of voice to help make a difference. Check out our tips here.
|
 |
4 reasons why IM is the front line for organizational culture and leadership
The more you communicate, the stronger your organizational culture will be. Here's how instant messaging makes that happen.
|
 |
4 disadvantages of the grapevine and when to use IM to talk to employees
You can't stop people from participating in the grapevine, but you *can* have more control over how your teams communicate. Here's how.
|
 |
Trillian 6.4: GIFs, new presence options, and more
Happy new year! We're kicking off 2021 with a new Trillian release featuring a batch of new features and fixes. Read on to see what's new! 🥂
|
 |
The pros and cons of real-time vs. asynchronous communication
What's the difference between real-time and asynchronous communication, and why do they both suit different situations?
|
 |
What communication channels should you have in your comms toolkit?
With so much to choose from, it can be difficult to decide which internal communication channels are right for your company. Let's look at your options.
|
 |
Best practices for nurses: Using tech to update families with critical health news
Research has shown that when healthcare providers keep patients and their families well-informed, there's a decrease in ER visits and faster recovery. Here's how to do it with tech.
|
 |
Bedside manner over IM: how to keep a personal touch while remaining safe
Instant messaging can't replace face-to-face communications, but nurses and other healthcare workers can maintain a personal touch with these quick tips.
|
 |
30 things you need to know about instant messaging for business
Instant messaging has been around for many years now, but what's it all about? Here's a list of things you need to know about IM for business.
|
 |
The small clinic’s step-by-step guide to making a crisis management plan
When you're in a difficult situation, it's important to have a plan in place to deal with it. Here is our step-by-step guide to creating your own crisis management plan.
|
 |
3 tasks healthcare professionals can automate on IM during an emergency
In this blog, find out the three essential tasks healthcare professionals can automate on IM during an emergency.
|
 |
4 remote working and collaboration tips for healthcare suppliers
Are you a healthcare supplier working from home? Here are four remote working and collaboration tips that may be worth considering.
|
 |
How healthcare AI can integrate with messaging to improve patient care
Artificial intelligence (AI) is progressing rapidly in the healthcare industry. Find out how AI and IM can work together to make your team more efficient.
|
 |
Building team accountability with IM
Team accountability can feel like a tightrope walk between trust and micromanagement. Instant messaging is often overlooked, but it can play a helpful role. Here's how.
|
 |
4 quick instant messaging tips for busy team leaders to get their message across
Team leaders and managers must communicate with their teams clearly and efficiently for their message to stick. Here's how instant messaging can help.
|
 |
5 tactful tips for communicating urgent updates in your group text app
Urgent messages are helpful but sometimes stress-inducing. Find out how to communicate urgent updates effectively with these 5 tips.
|
 |
4 pitfalls of introducing IM governance for risk and compliance
Find out how to master information governance for risk and compliance while avoiding a few of the most common pitfalls.
|
 |
How secure instant messaging can play a part in patient-centered care
Arm your healthcare staff with tools that elevate the importance of patient-centred care. Here's where instant messaging fits in.
|
 |
3 benefits HIPAA-compliant messaging can bring to hand-off communication
Communication errors can result in serious adverse events in healthcare. Here's how HIPAA-compliant messaging can improve patient hand-offs.
|
 |
Why data security is more vital than ever during this healthcare crisis
Data security is an afterthought for too many organizations. Bring data security out of the IT department and provide practical tips to your entire team.
|
 |
10 practical ideas for being a good boss on your instant messenger app
Positive reinforcement is an important part of managing a team. A great way to boost morale is by being a good boss on your instant messenger app.
|
 |
3 kinds of business communication software that define working in 2020
There are many factors to consider when settling on the right business communication software. Here, we outline the 3 kinds that define business in 2020.
|
 |
Can you replace your next boring business meeting with instant messaging?
Unnecessary meetings cost businesses billions each year. Here's how to tell when instant messaging should take their place.
|
 |
Say hello to the brand new Trillian 6.3! ✨
We've added lots of great new features and security improvements in Trillian 6.3. Keep reading to dive into the latest and greatest coming your way in this exciting new release!
|